How to install SecurID MFA for Linux PAM authentication. This guide is useful for legacy RSA Authentication Agent for PAM estates, but current deployments should compare it with the newer SecurID MFA Agent for UNIX documentation before changing production login policy.
TL;DR
- Back up every PAM file before adding
pam_securid.so. - Keep a separate root session open until SSH, console login, and rollback are tested.
- Use this article for legacy RSA/SecurID PAM agents; use the current SecurID MFA Agent docs for new deployments.
Source check – May 10, 2026: SecurID publishes current MFA Agent for UNIX documentation, including PAM installation guides for Oracle Linux, RHEL, Ubuntu, CentOS, and Rocky Linux. The older RSA SecurID Authentication Agent 8.1 for PAM guide remains the right context for legacy agent estates.
| Topic | When | Command or source |
|---|---|---|
| PAM backup | Before editing login policy | sudo cp -a /etc/pam.d /root/pam.d.backup |
| Agent docs | New deployments | SecurID MFA Agent for UNIX |
| Rollback | Failed login test | Restore the PAM service file from backup |
Start here: If you need general Linux MFA rather than an RSA/SecurID estate, compare this guide with Google Authenticator MFA on Linux. If you are protecting SSH specifically, keep the SecurID SSH configuration guide open as the next step.
What is RSA?
Thanks for stopping by turbogeek.co.uk, be sure to check out my other content by clicking here.
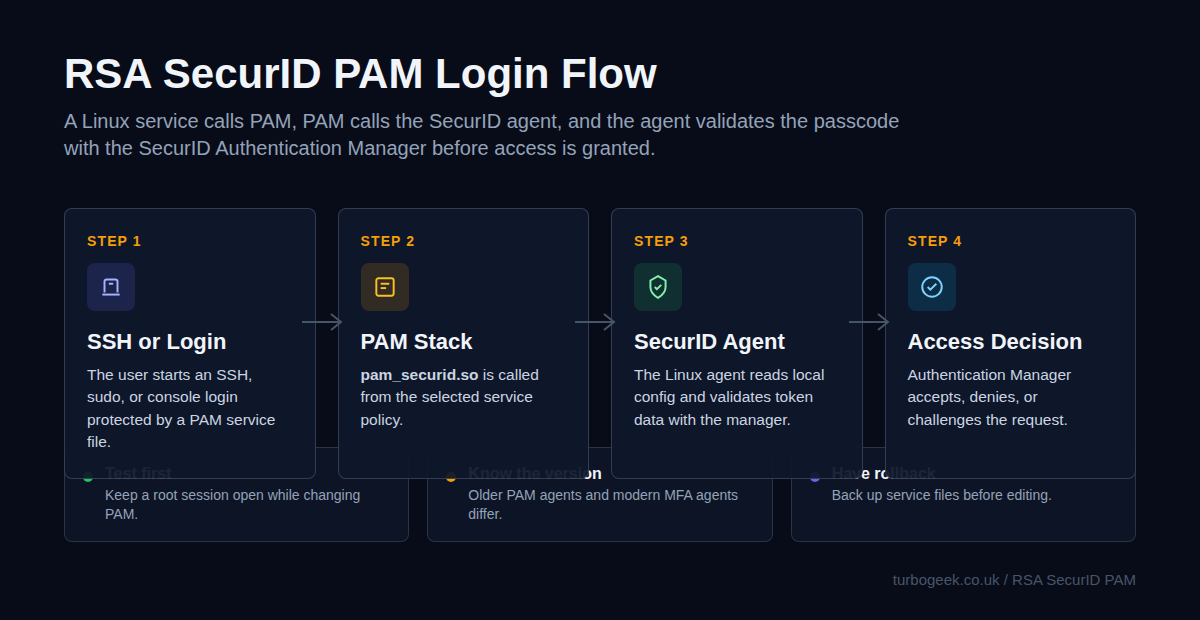
SecurID authentication access is essential in many enterprise deployments. It creates an additional layer of protection for server infrastructure by adding multi-factor authentication. This guide focuses on SecurID access for Linux PAM. To make a successful legacy installation, you require SecurID Authentication Manager infrastructure and an agent installed on each protected server.
With a strong RSA authentication appliance, users can control their own access management using a mobile device or a downloaded RSA desktop application.
The RSA Secure ID access Agent is available for the following Operating Systems, Please note that Windows is supported, but I will be focusing on Linux only in this guide:
- Red Hat Enterprise Linux (RHEL) RHEL 6.8 – 6.10 (32-bit and 64-bit)
- RHEL 7.1 – 7.5 (64-bit)
- CentOS CentOS 7.5 (64-bit)
- Oracle Linux Oracle Linux 6.8 – 6.10 (64-bit)
- Oracle Linux 7.3 – 7.5 (64-bit)
- SUSE Enterprise Linux SUSE Enterprise Linux Server version 11 SP3 – SP4 (32-bit and 64-bit)
- SUSE Enterprise Linux Server version 12 – 12 SP3 (64-bit)
- SUSE Linux Enterprise Server 15 (64-bit)
- Solaris Solaris SPARC 10 (32-bit and 64-bit). RSA recommends Update 8 or later.
- Solaris SPARC 10.5 (32-bit and 64-bit) with Zones
- Solaris SPARC 11.2 (32-bit and 64-bit)
- Solaris x86 10.5 Update 11 (32-bit)
- Solaris x86 11.2 (32-bit)
- AIX AIX 7.1 TL3 (SP5) Power 6 (32-bit and 64-bit)
- AIX 7.2 TL1 (SP2) Power 8 (32-bit and 64-bit)
How to install RSA SSO Agent on Linux Distributions
Please note : This process has been installed and tested on RedHat 6.9 (Santiago), RedHat 7.3 (Maipo) and CentOS 7.4.
This service allows for two-factor authentication using an RSA passcode and user password.
Step 1 – Installation Prerequisites:
Please take some time to read and understand the prerequisites of the RSA agent installation:
- The User must have an account on the Linux Server
- After Installation, changes must be made to the following files (outlined later), access via root or sudo privileged user:
/etc/ssh/sshd_config
/etc/pam.d/sshd
/etc/sd_pam.confStep 2 – Configure the RSA SecurID Authentication Server
Log onto your RSA Appliance server and complete the following tasks:
- The LINUX server IP address MUST be manually added to the RSA Authentication server.
(In the security console, click Access > Authentication Agents > Add New)
- A copy of the RSA Authentication Manager certificate is required.
(In the security console, click Access > Authentication Agents > Download Server Certificate File)
- Generated Configuration File (AM_Config.zip) from the RSA Security Console.
(In the security console, click Access > Authentication Agents > Generate Configuration File)
Please Note – To speed up the process I recommend unzipping the AM_Config.zip that is downloaded as part of the above tasks, do this before you transfer to the server
Step 3 – Transfer the Installation files and config to the Linux Server
Transfer your files to the Linux server. You may wish to do this using SCP or some form of FTP client, such as FileZilla or WinSCP. If you are using macOS, I recommend The Unarchiver
RSA PAM package (PAM-Agent_v8.0.0.195.11_23_17_04_55_23.tar)
(https://community.rsa.com/community/products/securid/authentication-agent-pam)
Step 4 – Prepare the Linux Server
Log onto the Linux server using SSH. Preferably with a sudo root account
Create /var/ace directory on the server host
mkdir /var/aceCreate the Authentication Manager configuration file, sdopts.rec
touch /var/ace/sdopts.recAdd the server host IP address to the sdopts.rec
sudo vim /var/ace/sdopts.recThe sdopts.rec file only needs one line
CLIENT_IP=x.x.x.x
where IP is the IP of the host machine
Copy the server.cer and sdconf.rec files to /var/ace folder
sudo cp server.cer sdconf.rec /var/aceInstall two packages to the server to ensure the RSA PAM package will work.
sudo yum install selinux-policy-develsudo yum install policycoreutils-python Please note – the second package (policycoreutils-python) should be installed as part of the install process of the first package. This can be verified during the install process of the selinux-policy-devel package.
Step 5 – Install the PAM Authentication Agent
To Install Pam RSA Agent V8.0 or greater, browse to the downloaded path you set in Step 3 (for example,/tmp/)
Extract the PAM Agent tar file
tar xvf PAM-Agent_v8.0.0.195.11_23_17_04_55_23.tarNavigate to the newly created folder and install the agent
For Example:
cd PAM-Agent_v8.0.0.195.11_23_17_04_55_23
sudo sh ./install_pam.shYou will now be asked to accept a license agreement. Scroll to the end of the agreement (space bar). Type A to accept. Press RETURN. During the installation, you will be asked a series of questions regarding the install path, authentication mode and
- Select which operation mode you would like to
configure for authentication [0/1/2] :
Choose option 0 (RSA Authentication Manager with the UDP Protocol) - Enter Directory where sdconf.rec is located [/var/ace] :
<RETURN> (the sdconf.rec file should be located in the /var/ace folder from previous step) - Please enter the root path for the RSA Authentication Agent for PAM directory [/opt] :
<RETURN>
Once successful, the install will output the following:
The RSA Authentication Agent for PAM 8.0.0 [195] will be installed in the /opt directory.
pam/
pam/conf/
pam/conf/mfa_api_template.properties
pam/conf/log.properties
pam/lib/
pam/lib/32bit/
pam/lib/32bit/libpamrest32.so
pam/lib/32bit/liblog4cxx.so.10.0.0
pam/lib/32bit/pam_securid.so
pam/lib/64bit/
pam/lib/64bit/liblog4cxx.so.10.0.0
pam/lib/64bit/libpamrest.so
pam/lib/64bit/pam_securid.so
pam/bin/
pam/bin/32bit/
pam/bin/32bit/acetest
pam/bin/32bit/ns_conv_util
pam/bin/32bit/acestatus
pam/bin/64bit/
pam/bin/64bit/acetest
pam/bin/64bit/ns_conv_util
pam/bin/64bit/acestatus
Checking /etc/sd_pam.conf:
VAR_ACE does not exist - entry will be appended
OPERATION_MODE does not exist - entry will be appended
RSATRACELEVEL does not exist - entry will be appended
RSATRACEDEST does not exist - entry will be appended
ENABLE_USERS_SUPPORT does not exist - entry will be appended
INCL_EXCL_USERS does not exist - entry will be appended
LIST_OF_USERS does not exist - entry will be appended
PAM_IGNORE_SUPPORT_FOR_USERS does not exist - entry will be appended
ENABLE_GROUP_SUPPORT does not exist - entry will be appended
INCL_EXCL_GROUPS does not exist - entry will be appended
LIST_OF_GROUPS does not exist - entry will be appended
PAM_IGNORE_SUPPORT does not exist - entry will be appended
AUTH_CHALLENGE_USERNAME_STR does not exist - entry will be appended
AUTH_CHALLENGE_RESERVE_REQUEST_STR does not exist - entry will be appended
AUTH_CHALLENGE_PASSCODE_STR does not exist - entry will be appended
AUTH_CHALLENGE_PASSWORD_STR does not exist - entry will be appended
BACKOFF_TIME_FOR_RSA_EXCLUDED_UNIX_USERS does not exist - entry will be appended
Checking /var/ace/conf/mfa_api.properties:
REST_URL does not exist - entry will be appended
CLIENT_KEY does not exist - entry will be appended
CA_CERT_FILE_PATH does not exist - entry will be appended
CLIENT_ID does not exist - entry will be appended
CONNECT_TIMEOUT does not exist - entry will be appended
READ_TIMEOUT does not exist - entry will be appended
MAX_RETRIES does not exist - entry will be appended
*****************************************************************************
* You have successfully installed RSA Authentication Agent 8.0.0 [195] for PAM
*****************************************************************************Please note: If SELinux is enabled, the output may include SELinux-related information.
Step 6 – Configure PAM
Change /etc/pam.d/sshd
vi /etc/pam.d/sshdAdd the following lines to the sshd
Bashauth required pam_securid.so auth required pam_unix.so
Using # rem out other auth required lines (for example)
Bashauth required pam_sepermit.so
Change the sshd_config file
vi /etc/ssh/sshd_configSet the following parameters and save the changes:
PasswordAuthentication no
ChallengeResponseAuthentication yes
UsePAM yes
UsePrivilegeSeparation no
**Please note: This file may look different with each version of Linux and also whether SELINUX is enabled **Change the /etc/sd_pam.conf file
vi /etc/sd_pam.confBashENABLE_USERS_SUPPORT=1 LIST_OF_USERS=root PAM_IGNORE_SUPPORT_FOR_USERS=1 PAM_IGNORE_SUPPORT=1
Once you modified the above files restart the SSHD service
IMPORTANT NOTICE:
DO NOT close the terminal / SSH window! If there is a misconfiguration you could potentially lock yourself out of the system altogether**
To restart the service in Red Hat 6
service sshd restart To restart the service in Red Hat 7
sudo systemctl restart sshd.serviceStep 8 – Testing
During the installation, the PAM installer will add the following scripts to /opt/pam/bin/64bit:
./acestatus
./acetest
./ns_conv_utilTo test the RSA Authentication module, type:
./acetestYou should be presented with:
Enter USERNAME:
(E.G Joe.Bloggs)
Enter PASSCODE:
(using your RSA soft
token enter your PIN and generated CODE)
If all of the details are entered correctly, you should receive the following message.
Authentication Successful.
Step 9 – Live Tests
Once you have achieved a successful test status, open up a new SSH session to test the two-factor authentication. During this phase, you should be asked to enter your:
USERNAME: PASSCODE : PASSWORD
You should now have gained access to the required server.
Troubleshooting:
If your testing was unsuccessful, please check the following logs
Cat or tail /var/log/secure to view the RSA logs
tail –f /var/log/secureReview the entries within the log to ensure the details you enter are correct.
If your “live” login fails, the logs within the RSA Security Console can be reviewed using the Authentication Monitor.
Adding Exceptions:
There are many circumstances where you will need to give a user account an exception, such as the root account, a backup service or any other system service that needs sudo root access.
Note the entry within the /etc/sd_pam.conf file
vim /etc/sd_pam.confLook for the line
LIST_OF_USERS=root
This section allows you to enter system users that shouldn’t require two-factor authentication. The above example shows the root user. This is list can contain as many users as necessary
Important: Users must be separated by a colon :
For Example:
LIST_OF_USERS=root:nagios:contabuser
Certain system functions may require access to the root user (RSYNC for example), it would be beneficial to exclude this user.
That’s it, thanks for taking the time to read this article. if you have any questions or feedback please write in the comment section below.


Leave a Reply