TL;DR – Rust core tools
- Ubuntu 26.04 makes rust-coreutils and sudo-rs part of the default path: Canonical also keeps the original implementations around for compatibility.
- Most people will not notice interactively: the real scrutiny belongs on old scripts and weird flags.
- The right response is test coverage, not panic: validate your automation and keep a fallback plan.
- If a script depends on edge behaviour, now is the time to find out.
Start here: If your main concern is automation risk, jump straight to the testing section and keep Linux File Management Cheat Sheet nearby if you want a quick reminder of which core commands your estate actually leans on most often.
| Topic | When | What to do |
|---|---|---|
| Interactive shell use | You type normal commands manually | You will probably notice little. |
| CI scripts | You use coreutils in pipelines | Run targeted validation before rollout. |
| Old admin scripts | They rely on odd flags or parsing | Assume nothing and test them. |
| Security review | You care about memory-safe defaults | This release is worth attention. |
Canonical says Ubuntu 26.04 makes rust-coreutils the default core utility set and sudo-rs the default sudo implementation, while keeping the traditional implementations available for compatibility and fallback. That is a big platform statement, even if the average terminal session looks unchanged at first glance.
The only useful question for admins is whether the new defaults break assumptions that your estate forgot it had. Interactive command use is rarely the issue. Old scripts, unusual flags and brittle parsing are where the truth lives.
Why most admins will barely notice day to day
If your normal shell life is ls, cp, mv, cat, sudo and friends in familiar ways, the new defaults may feel invisible. That is by design. The whole point of a distribution making this sort of move is that the surface stays familiar while the implementation underneath becomes safer.
That is also why you should not judge the change purely by whether your terminal prompt looks different after lunch. The real test is behavioural compatibility under automation.
Where you might notice the difference
Scripts that depend on unusual flags, parse command output in brittle ways, or rely on corner-case behaviour are the obvious risk zone. If you have shell scripts that nobody touched in years because they ‘just work’, those deserve fresh eyes before you make this release your default build.
sudo-rs also deserves some targeted validation anywhere you have unusual sudoers policy or operational wrappers around sudo. Canonical keeping a fallback path is useful, but the fallback only helps if you detect the issue early.
- Look for parsing of human-readable command output instead of machine-friendly flags.
- Look for little shell helpers nobody thinks about until they fail at 2am.
- Look for privilege escalation wrappers or policy assumptions around sudo behaviour.
How to test this sensibly
You do not need a giant programme to validate this change. Start with the scripts that touch files, process output, or run as part of provisioning and incident response. Run them in CI or on a disposable 26.04 box and inspect where behaviour diverges.
The fallback story is useful, but it should be an exception path, not your first plan.
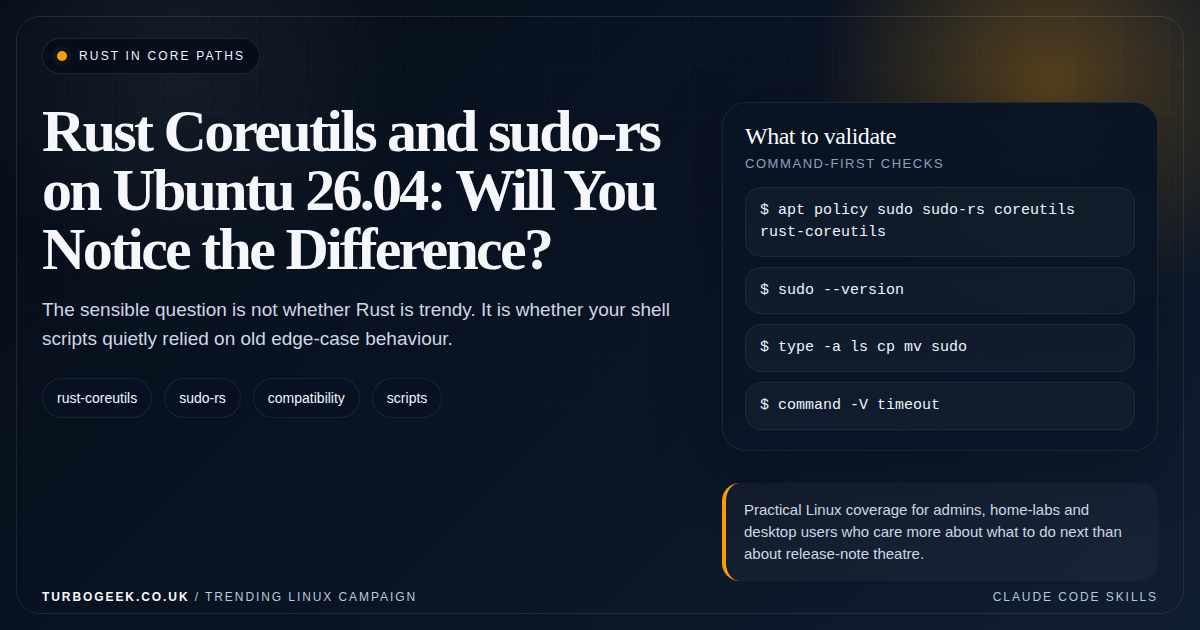
# Inspect the package and command path choices on Ubuntu 26.04
apt policy sudo sudo-rs coreutils rust-coreutils
sudo --version
type -a ls cp mv sudo
command -V timeoutThe practical call
Ubuntu 26.04’s Rust-based defaults are worth taking seriously because they move memory-safety work into the everyday system path. They do not justify blanket fear. They justify disciplined testing in the few places where behavioural compatibility truly matters.
That means shell scripts, provisioning flows and privilege boundaries. Keep the security article in this batch next to this one, and use Linux File Management Cheat Sheet if you want a quick refresher on the commands most likely to be involved.