TL;DR – CrackArmor on Ubuntu
- Canonical published guidance on March 12, 2026: eleven patches addressed nine vulnerabilities in the AppArmor story.
- The company explicitly recommends both kernel and userspace updates: one without the other is not the full response.
- All of the issues require unprivileged local user access: that does not make them optional if you run multi-user systems or risky workloads.
- Check the running kernel and AppArmor state after patching.
Start here: If you only need the action plan, jump straight to the verification section below and keep Linux SSH Hardening Checklist or your normal hardening checklist nearby so this becomes part of routine hygiene rather than one-off drama.
| Topic | When | What to do |
|---|---|---|
| Single-user lab | Low user exposure | Patch anyway, but urgency is easier to sequence. |
| Shared server | Local users or many workloads | Treat this as a higher-priority maintenance item. |
| Desktop fleet | Many endpoints | Push kernel and userspace updates through normal channels quickly. |
| Compliance environment | You need evidence | Capture update state and verification output. |
Canonical’s March 12, 2026 AppArmor blog is refreshingly direct: Qualys disclosed the issues referred to as CrackArmor, Canonical published eleven patches for nine vulnerabilities, and the recommendation is to install both Linux kernel security updates and the relevant userspace mitigations.
That is the whole operational story in miniature. Understand scope, patch what actually needs patching, and verify the system state after the fact. The temptation to stop at ‘we ran updates’ is exactly how security gaps linger.

What the disclosure actually means
Canonical says all of the vulnerabilities require unprivileged local user access. That matters for prioritisation, but not in the lazy way people sometimes think. Plenty of Ubuntu machines are shared, multi-user, container-heavy, or exposed enough internally that local-user assumptions matter a lot.
The same post also makes an important point that many admins miss during vulnerability cycles: kernel-side fixes are only part of the answer when userspace mitigations are also part of the guidance.
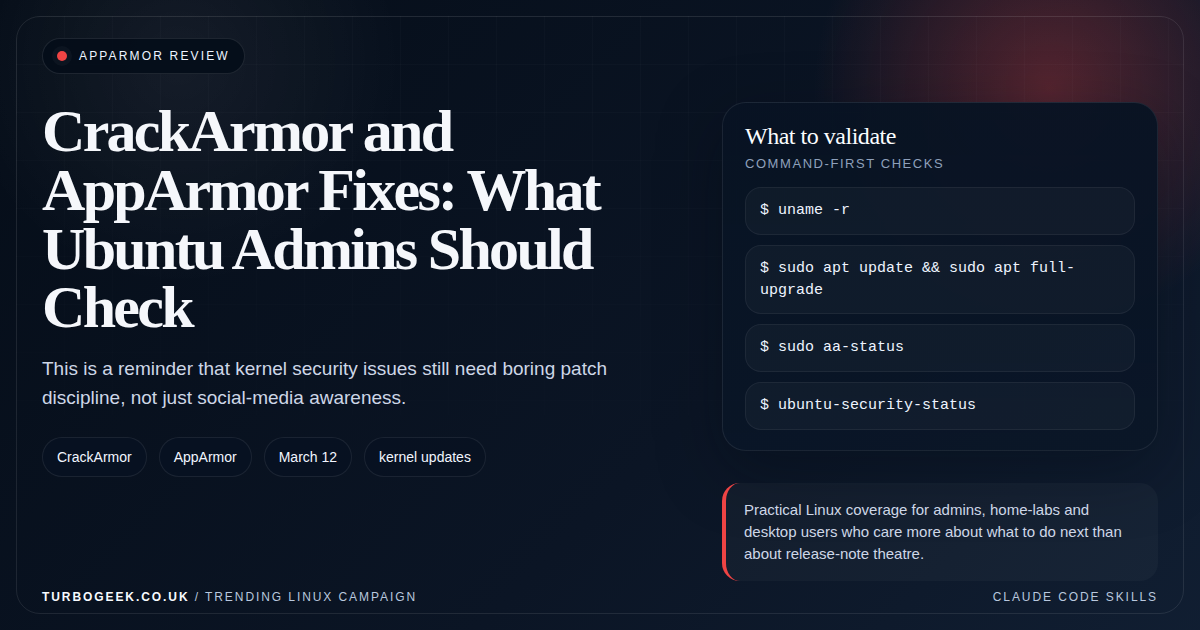
What Ubuntu admins should do first
Make sure you are actually pulling in the security updates, then make sure the running kernel is the updated kernel, not just a package you installed before lunch and never rebooted into. After that, verify AppArmor state and check whether any hosts are lagging on expected update channels.
The response should look boring and mechanical. That is a feature, not a weakness.
Why AppArmor still deserves attention
Mandatory access control systems are easy to under-appreciate because they mostly matter when something else goes wrong. That is exactly why AppArmor update discipline matters. Its job is to reduce blast radius when the rest of the day goes sideways.
CrackArmor is a useful reminder that host confinement is not dusty theory. It is live platform security work.
- Patching AppArmor-related issues is part of base-platform maintenance, not specialist hobbyism.
- Shared systems deserve more urgency than people often give them.
- Verification matters because package state and running state are not the same thing.
The practical close
Ubuntu admins should read the CrackArmor cycle as a cue to tighten routine patch hygiene, not as a one-week panic event. Install the kernel update, install the userspace mitigation, verify the running state, and move on with a little more discipline than before.
If you want the wider Ubuntu 26.04 security context around this, the 26.04 security article in this batch is the next logical read.
Related next steps
- Linux SSH Hardening Checklist
- Ubuntu Server First 30 Minutes: The Setup Checklist I’d Use Every Time
- Free Up Disk Space on Linux Quickly
- Ubuntu 26.04 LTS Security Changes That Actually Matter
- Real-time Ubuntu Is Free in 26.04: Who Should Actually Use It?
- Rust Coreutils and sudo-rs on Ubuntu 26.04: Will You Notice the Difference?